Telecommunications is an inherently data-driven industry. Traditionally, great focus has been placed on gaining data visibility into the core and transit areas of the network. This approach has provided valuable insights for throughput optimizations, speed, and general performance.
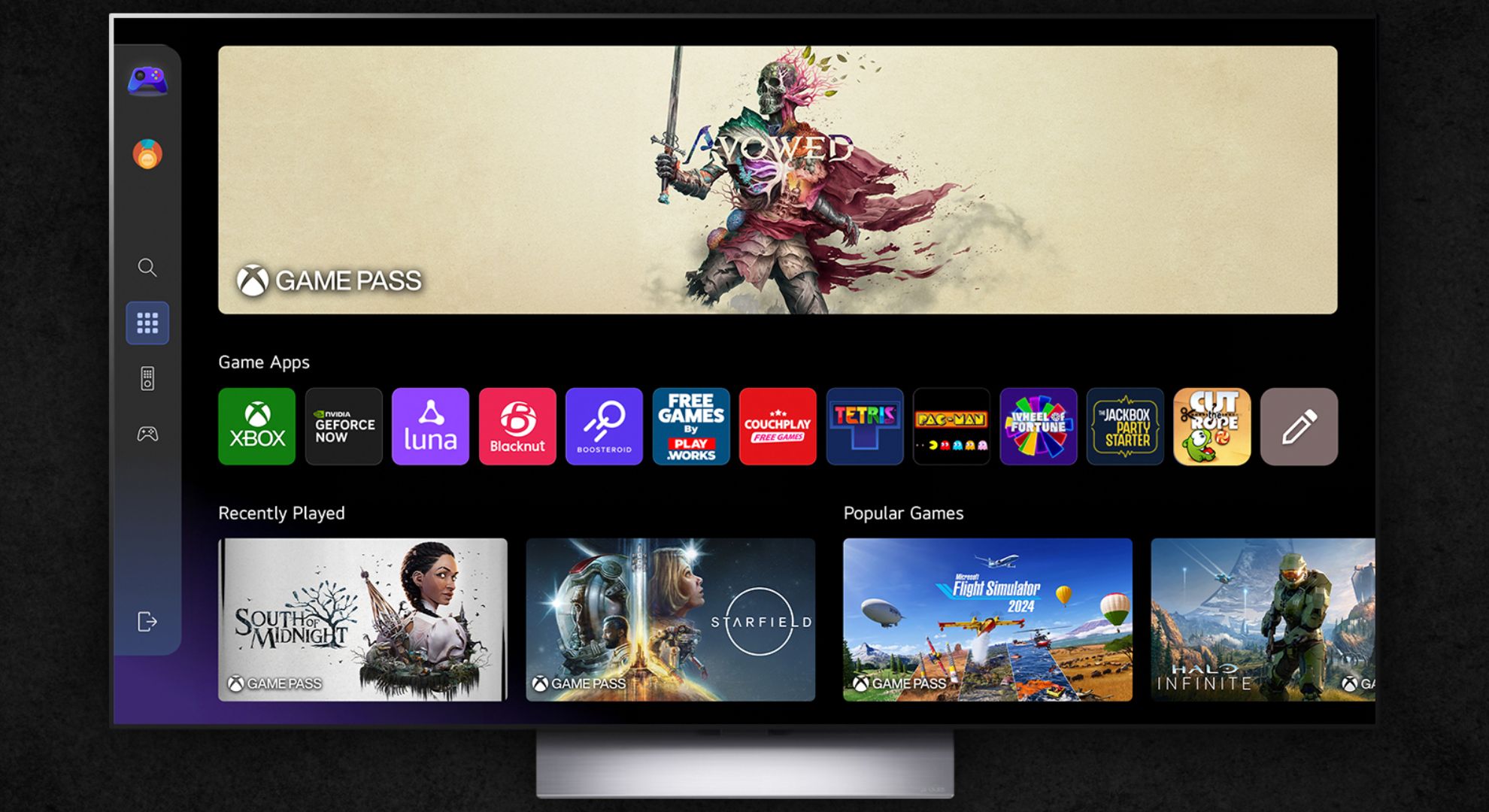
Regardless of promises of speed, customers are mainly concerned about whether or not they’re able to watch streaming services, play live games, and connect with colleagues and loved ones via video calling - sometimes simultaneously. To solve for optimized performance and a great customer experience, telecommunication companies are shifting their focus toward further enhancing their last-mile visibility.
Historically, service providers have used the last-mile data they collect to identify the worst-performing connections and pinpoint the group of customers most at risk of churning to another provider. However, if approached correctly, last-mile performance intelligence can offer more than just a way to mitigate churn.
Today, when consumers visit the marketing and sign-up pages of telcos or internet service providers, they are typically presented with maps showing broad network coverage and similar pricing between providers, indicative of both the competitiveness of the telecommunications landscape and the utility-like nature of many of its services. On paper, there is often little to differentiate providers from a marketing perspective.
This is where the opportunity lies. Service providers are in a unique position by virtue of owning and operating the networks that connect users with the applications and services they’ve come to rely on in their daily lives. By rethinking their relationship with last-mile data, additional benefits - beyond customer retention - are ripe for the taking when it comes to intelligent fault diagnosis, customer communication, and differentiated services.
How incomplete last-mile data can impact decisions
One of the most important aspects of data-driven decision-making is that the source data underpinning the decision is clean, comprehensive, and has good lineage. This goes to its quality and reliability as the foundation for decision-making.
With more comprehensive last-mile data, service providers and carriers can make better informed decisions regarding new product launches, network planning, capacity, and capital allocation. For example, telcos and service providers will make significant moves around optimization of services for the needs of specific market segments - such as gaming, or industrial companies with IoT needs, and so on.
This kind of optimization has long been a promise of network slicing technology, and many telcos and providers now have this in their arsenal. Yet, the biggest challenge may be determining the best customer cohorts to target with this level of optimized services. This is a problem that is addressable in part by having more comprehensive last-mile data to analyze and base these decisions on.
Incomplete last-mile data also makes it harder to determine where a proposed investment in network infrastructure or capacity would have the biggest performance improvement. By contrast, in circumstances where the telco or service provider is collecting last-mile data from every active service, from every home or premises, they have a much more comprehensive understanding of how their services land, and where improvements most need to be made.
Last-mile intelligence as a differentiator
Telcos and service providers have always had options available to them to collect last-mile data: whether that’s TR-069 on customer premises equipment, or specific broadband monitoring boxes.
The key opportunity ahead lies in the improved capability within service provider environments to correlate and use last-mile intelligence.
For instance, last-mile network intelligence can significantly enhance the ability to deploy maintenance strategies proactively. By continuously monitoring the last-mile connections, service providers can identify potential issues before they escalate into major problems, reducing downtime and improving overall service reliability. This proactive approach not only helps in maintaining customer satisfaction but also reduces operational costs associated with emergency repairs and customer support.
Service providers can also use last-mile insight to analyze usage patterns and preferences to tailor their offerings for a higher level of personalization that can lead to deeper customer satisfaction and loyalty, as customers feel their specific needs are being met.
In a market where pricing and coverage are often similar, last-mile intelligence can be a key differentiator. Service providers that can demonstrate superior last-mile performance through transparent reporting, value-add services, and customer testimonials can gain a competitive edge. This transparency builds trust and can be a deciding factor for customers choosing between providers.
Where will richer data take you?
With insights into all last-mile connections, service providers can access a valuable dataset that has long been overlooked. This knowledge can enhance customer experience and inform a wider range of commercial decisions, resulting in comprehensive strategies that are supported by a clearer understanding of the last-mile situation and the needs of their subscribers.
We rate the best network monitoring tool.
This article was produced as part of TechRadarPro's Expert Insights channel where we feature the best and brightest minds in the technology industry today. The views expressed here are those of the author and are not necessarily those of TechRadarPro or Future plc. If you are interested in contributing find out more here: https://www.techradar.com/news/submit-your-story-to-techradar-pro
from Latest from TechRadar US in News,opinion https://ift.tt/vmuCPYc











0 coment�rios: